Risk Assessments
Our proven methodologies identify all threats, implement corrective measures, and ensure compliance with regulations for your complete protection.
Cyber Program & Security Strategy Assessment
- Assess and measure the efficiency and effectiveness of your cyber security program and its supporting controls.
Operational Risk Assessment
- By assessing and prioritizing the cyber and physical risks in your environments, we work with you to develop a plan to mitigate those risks together.
Cyber Posture Assessment
- Check your cyber posture against the external cyber threat landscape and internal threats.
Cyber Security Maturity Scoring
- Determine your current cyber security maturity using the U.S DOE Cybersecurity Capability Maturity Model (C2M2).
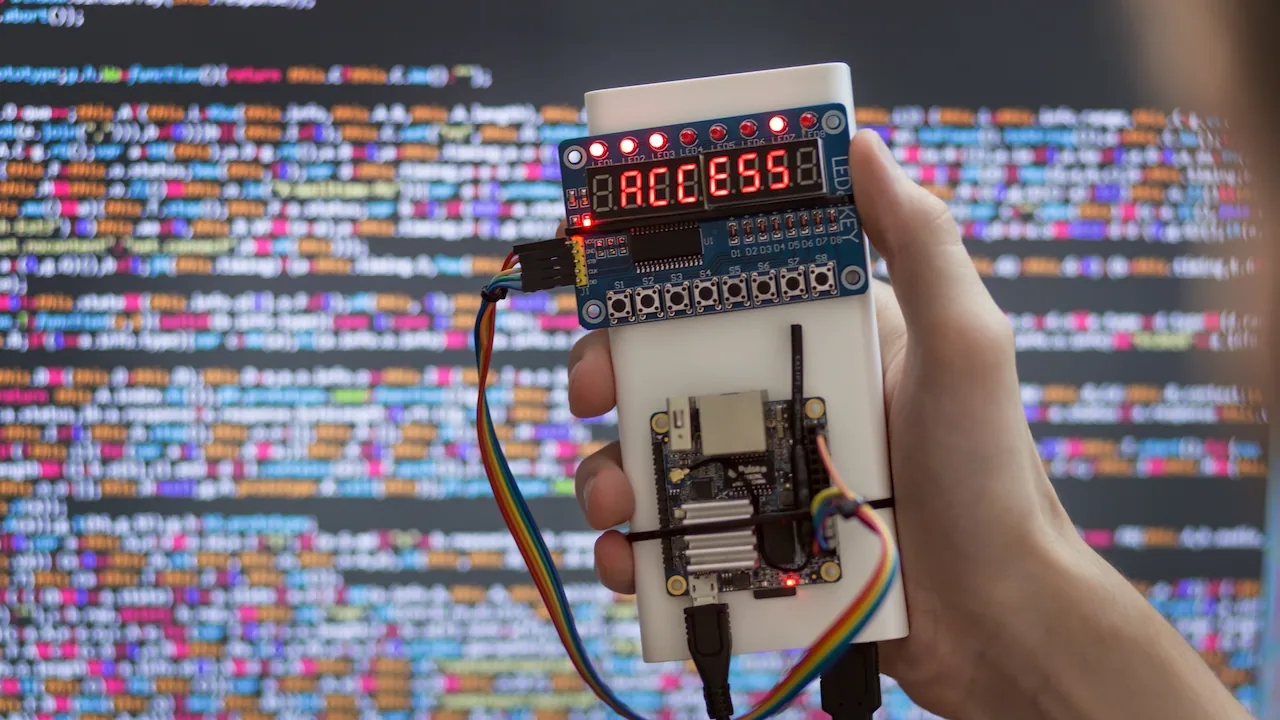
Cyber Vulnerability Assessment (CVA)
- Our vulnerability assessments align with industry cyber security standards and best practices to give you a clear picture of top vulnerabilities and their mitigation.
- Our physical security assessments analyze internal and external threats on your structures, equipment, business continuity, and operations for a 360-approach to safety.
Network Penetration Testing
- Our non-intrusive penetration tests measure the strength of your current security measures and detect vulnerabilities without impacting your operations.
NIST & Privacy Standards Assessments
- Identify gaps and stay up to code through assessments that integrate Generally Accepted Privacy Principles (GAPP) into the NIST Cybersecurity Framework.
Microgrid & DERs Cyber Assessment
- Acumen’s methodology addresses cyber security and physical security via the NIST Cybersecurity Framework, specifically tailored for your microgrids and DERs.
Advisory
Develop a comprehensive security management program that suits your unique entity best.
Business Case Development
Develop both cyber and physical security programs through ROI and cost-avoidance quantification.
Cyber & Physical Security Governance & Program Recommendations
Develop complete programs, including critical governance functions.
Security & Privacy Roadmaps
Gain useful insights through personalized roadmaps and tools for long-term security solutions.
Supply Chain / Third Party Cyber Security Risks
Assess, mitigate, and manage threat landscape risks associated with outside sources.
Network Architectural Reviews
Review IT and OT network architectures to identify gaps and potential risks to critical systems and environments.
Secure Network Architectures Development
Create secure IT and OT network architectures to ensure proper zoning and secure protection of your key systems and data.
Organizational Change Management Planning
Align your IT and OT groups with the required governing practices for a successful security program.
Cyber & Physical Security for Microgrids & DERs
Our security models can be used for operations of any size, given our past experience with NRECA.
Compliance Advisory
Our extensive experience providing compliance services for NERC, CIP, and the Ontario Cyber security Framework translates to providing you with expert advice, and compliance guidance.

Implementation Services
Manage and mitigate ever-evolving security threats with tailored strategies, roadmaps, and frameworks in the areas of guidance, technical solutions, and stable cyber architecture.
Workforce Transition
Take advantage of our temporary assistance for resource gaps as you adjust to new changes.
Policy, Standards & Procedures Development
Augment your policy library with updated Cyber & Physical Security and Privacy Policies, Incident Response, and Technical Procedures.
Cyber Incident Response Planning & Communications
Stay safe in every situation with fully developed Incident Response Plans, complete with scenario playbooks and communication plans.
Network Configuration & Segmentation
Configure and segment your IT and OT networks for maximum security while maintaining efficiency and operational effectiveness.
NERC Cyber Security CIP Standards
Guiding you through the standards landscape of Cyber Impact Rating Methodology & Determination (CIP-002), Cyber Security Tools & Systems (CIP-003 to 014), Supply Chain Risk Management (CIP-013), and Internal Response Planning & Communications.
Management Services
For all your unique security needs, Acumen guarantees cost-effective solutions for managing your cyber security resources across your utility.
Cyber Incident Response & Recovery Exercises
Heighten vigilance and security response amongst your cross-functional teams with our recovery exercises and testing program.
CISO-as-a-Service
No CISO? No problem! Acumen provides this function as a service for your benefit.
Cybersecurity Health Check
Assess your cyber security posture and maturity with our quick and inexpensive assessment methodologies.
Remediation Support
Get the results you need for your organization with our remediation guidance and hands-on approach to solving your problems.
Training Services
Our expert instructors offer training both on-site and at our office locations on important topics such as:
- Board/Executive Management Level Cybersecurity Training
- Fundamentals of IT/OT Cybersecurity Risk Management
- Intermediate IT/OT Cybersecurity